Research & Innovation
Researchers uncover that, by inhibiting specific trigeminal sensory neurons, pain from mechanical allodynia can be regulated.
Recent research reveals the impact of a specialized type of cognitive training developed by a UAB expert.
UAB researchers review how senescent “zombie” cells contribute to skeletal muscle weakness with aging and disease, outlining emerging therapies such as senolytics and senomorphics that could help preserve muscle health and extend health span.
Bmal1 has been revealed as an unexpected driver of diabetic vascular calcification, linking circadian signaling to arterial stiffening and cardiovascular risk and opening new therapeutic avenues.
Findings from this investigation could contribute to improved clinical interventions for patients recovering from pneumonia and help reduce the risk of long‑term heart damage.
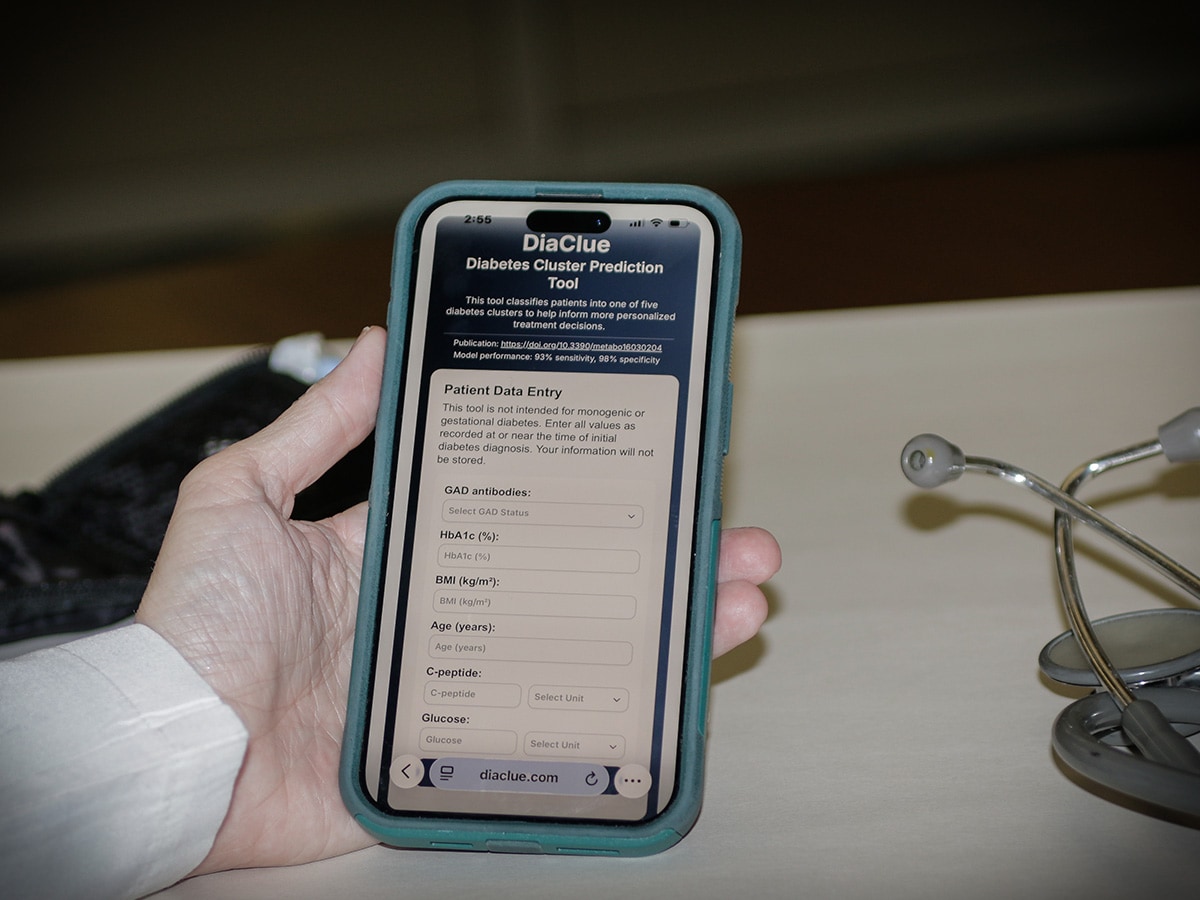
A digital app for clinicians developed by UAB researchers classifies diabetes into five subtypes, enabling more personalized treatment and better outcomes for patients.
UAB researchers have secured a patent for a novel lens design that could slow myopia progression in children, translating decades of vision science research into potential clinical therapies.
This is one of the few studies of its kind to look at the use of magnesium sulfate for babies born at 22-24 weeks of gestation in preventing neurodevelopmental outcomes.
UAB researchers demonstrated that GLP-1 receptor agonist use is associated with a lower risk of heart failure, dangerous heart rhythms and major cardiovascular events in patients with non-obstructive hypertrophic cardiomyopathy.
PreciPS identifies frontline frustrations before providing operational solutions in patient care.
Adolescents are analyzed through a period of transition into adulthood to help paint a better picture of how digital media use contributes to memory decline and suicide attempts, and shares how parents can mitigate these effects.
The study highlights the unmet need for effective strategies to prevent chemotherapy‑induced nerve damage, which affects long‑term quality of life for cancer survivors.
Recent innovations include a noninvasive external urine collection device, a system designed to simplify how clinicians manage fluid balance in critically ill patients, an ergonomic assist device for ureteroscopy and new ways to prevent kidney stones.
UAB is leading a national study examining how personalized genetic risk information can improve prevention of chronic diseases, helping guide earlier screening, treatment and clinical decision‑making.
UAB researchers discover the mechanism by which neurofibrillary tangles spread through the brain of Alzheimer’s patients is via connected neurons, and these findings reveal a major disease etiology that could lead to new therapies that slow Alzheimer’s disease progression.
The AMPLIFY Diet intervention helps older survivors of obesity-related cancers achieve meaningful weight loss and improvements in key health outcomes without in‑person visits, coaching calls or live counseling.
A new UAB study reveals how the eye creates sharp vision, showing that individual light-sensing cells in the retina send precise signals to the brain.
A rise in research funding within UAB’s Department of Family and Community Medicine highlights its expanding research impact.
A UAB professor leads a new discovery that could change how an aggressive thyroid cancer with limited treatments is approached and treated.
A new UAB study shows that a prevalent Meier‑Gorlin syndrome variant reduces ORC6 protein production — not its function — suggesting future treatments could boost protein levels to prevent developmental defects.
Patients who received the additional therapy showed a higher likelihood of surviving at both one month and three months after treatment.
UAB researchers are advancing cancer prevention and treatment through lifestyle-based survivorship care, adaptive molecular therapies and precision biomedical engineering.
This rare brain condition causes a person’s hand to move without intention or control.
New research from UAB shows a structured expert panel approach can accurately and reliably measure delirium severity in patients with and without Alzheimer’s disease and related dementias.
UAB has been a national leader in Fabry disease care and research for more than two decades.
The study is aimed to track early brain and child development in the United States by following pregnant participants and their children for approximately 10 years.
UAB researchers are developing a new at-home cervical cancer screening device aimed at increasing access to screening and improving early detection.
Scientists identify an immune switch, NFAT, that is crucial to successful pregnancies, offering new insights on the causes of preeclampsia, implantation problems and inadequate blood supply.
UAB scientists discovered an oral drug stopped weight rebound after discontinuation or cessation of GLP‑1 treatment in preclinical studies, opening the door to a new approach for maintaining weight loss.
The MajesTEC-3 clinical trial shows that using a new two-drug immunotherapy regimen can lead to long-lasting remission for patients with multiple myeloma. Over 83 percent of patients enrolled in the trial are alive and progression-free three years after therapy.