Get Help
AskIT is here to help. Submit a ticket through
this form
or email us at
Quick Resources
TechSolutions
Microsoft, Adobe, File Storage, Classrooms: UAB IT is here to support you.
2-Factor
2-Factor Authentication is required for all UAB students, faculty and employees.
Software
See UAB IT's entire catalog of software available for free and reduced prices.
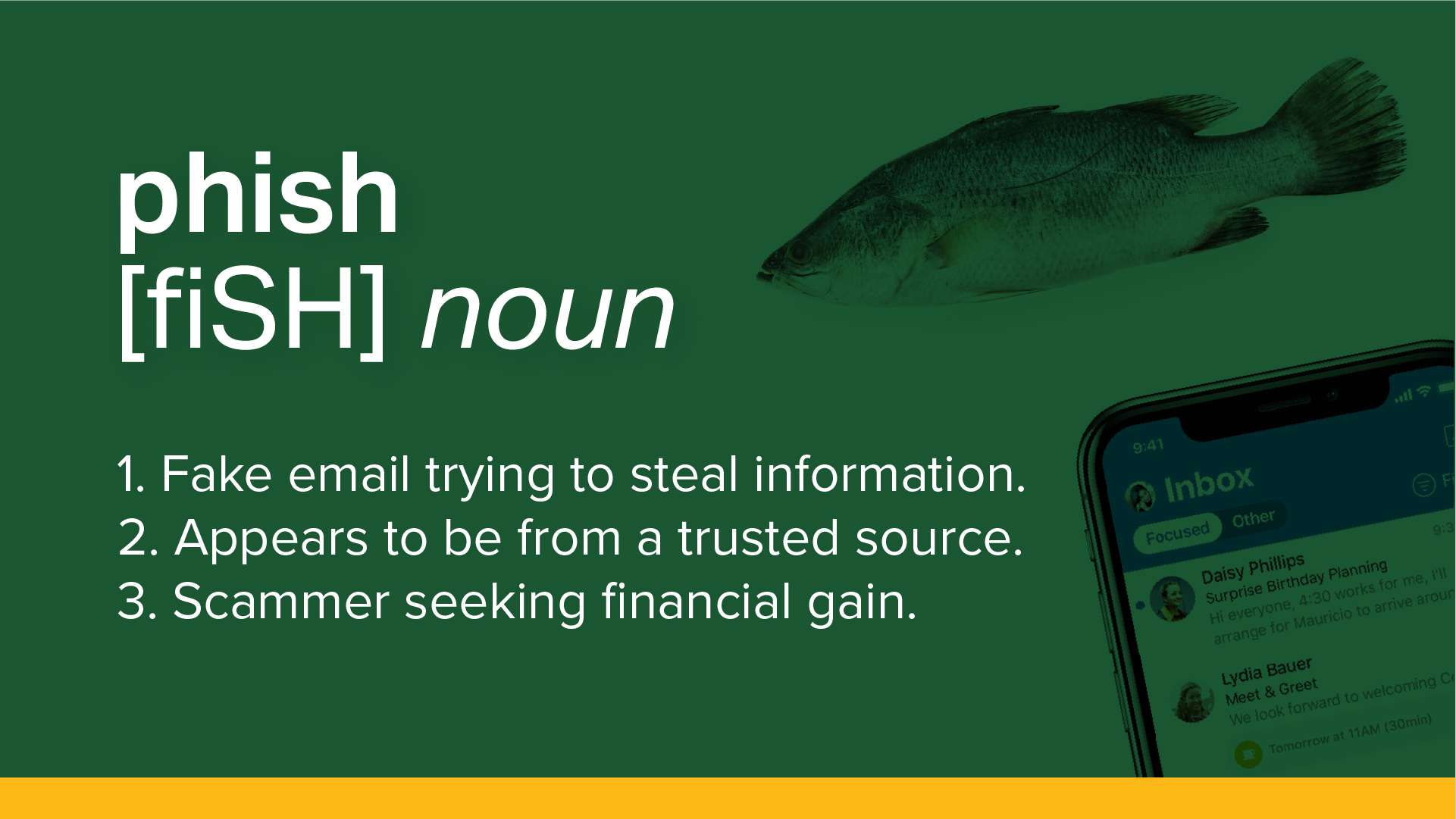
Security Awareness
Arm yourself with security knowledge to protect your personal data.
Policies & Guidance
Policies help keep everyone safe from malware, data thieves, and identity theft.
TechConnect
Purchase laptops and accessories for personal use with educational discounts.

Discover our organization's progress and accomplishments in our 2025 Annual Report. For real-time updates on our current successes, head to our Wins page, which tracks our achievements for 2025. Here, you can explore the efforts of our team members who have gone above and beyond to make a positive impact.